Data Privacy and Security Training
Empower your employees to proactively address privacy concerns and minimize the risk of violations under data privacy laws such as the GDPR and CCPA.
Get data privacy decisions right.
Traliant’s Global Data Privacy Awareness training prepares employees to recognize privacy risks, handle personal data responsibly, and respond appropriately when issues arise.
In a cinematic, TV-style format, it shows how routine workplace interactions, such as sharing files, accessing systems, or using AI tools, can quickly create privacy risks.
Built for real-world decision-making, this 30-minute course builds the awareness and judgment employees need to spot warning signs and take the right action. In these moments, learners are equipped to:
- Recognize how personal data is collected, used, and shared
- Identify privacy risks before they become incidents
- Understand data subject rights and when to escalate requests
- Apply key principles like Privacy by Design in daily work
- Handle data responsibly across systems, teams, and tools
The result: fewer mistakes, stronger data protection, and more defensible global compliance.
Organizations can further strengthen outcomes with additional training components designed to reinforce and sustain behavior change over time. A 12-minute refresher course helps reinforce key concepts after initial training, while short, 2-minute Data Privacy Micro Reels provide focused, in-the-moment reinforcement to support real-world application.
ONLINE TRAINING
Global Data Privacy Awareness
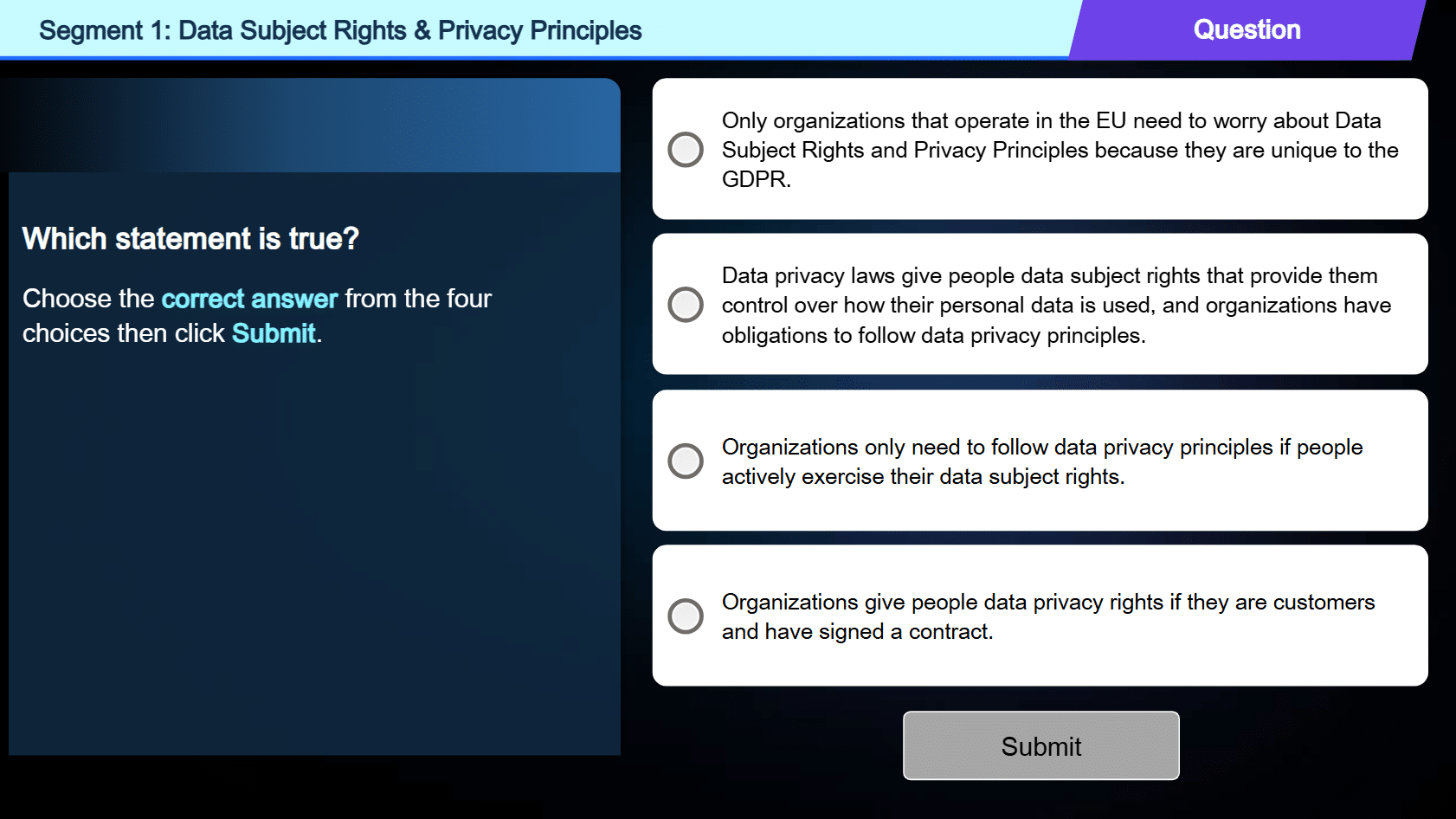
The course prepares employees to handle the most common and high-risk data privacy situations. What this course covers:
- What qualifies as personal data, including special category, anonymized, and pseudonymized data
- How global privacy laws like GDPR and CCPA apply to everyday work
- Core data privacy principles and why they matter
- How to recognize and respond to data subject rights requests (DSARs)
- How to handle personal data securely in the workplace
- The difference between data privacy and data security
- How AI tools impact data privacy obligations
- When and how to report a data privacy incident
What laws are covered by this course?
- General Data Protection Regulation (GDPR)
- California Consumer Privacy Act (CCPA)
- Quebec’s Law 25
- Over 160 Global National Level Privacy Laws
What to consider when choosing the most effective Data Privacy training
- Minimize legal and financial risks: Data breaches can result in costly fines, lawsuits, and damage to a company's reputation. Training helps organizations to comply with data privacy laws and to protect themselves from these risks.
- Promote a culture of data protection: Training helps to create a culture where employees understand the importance of protecting sensitive data and to follow best practices for handling and storing this information.
- Build trust with customers and stakeholders: Data privacy is becoming increasingly important to customers and stakeholders. Training helps organizations to demonstrate their commitment to responsible data handling.
- Empower employees: Training provides employees with the knowledge they need to understand the company's data privacy policies and to make informed decisions about how to handle sensitive data.
- Strengthen your organization's security posture: Training helps to build a strong security culture, making it more difficult for cybercriminals to succeed.
- Reduce the risk of costly data breaches: Data breaches can have a significant financial and reputational impact on organizations. Training can help to minimize these risks.
- The General Data Protection Regulation (GDPR): This law, enacted by the European Union, is a comprehensive data privacy law that applies to organizations that collect personal data of individuals located in the EU, regardless of where the organization is located.
- The California Consumer Privacy Act (CCPA): This law gives California residents certain rights regarding their personal information.
- The Health Insurance Portability and Accountability Act (HIPAA): This law protects the privacy of individually identifiable health information.
- Follow company policies: Be aware of the company's data privacy and security policies, and follow them carefully.
- Use strong passwords: Create complex passwords and don't reuse them across different accounts.
- Be cautious about phishing attacks: Be wary of emails and messages that ask for personal information or contain suspicious links.
- Protect your devices: Use strong passwords and encryption for your devices, and report any suspicious activity immediately.
- Be aware of the data you're handling: Understand what types of data you are working with and the level of sensitivity.
- Limit access: Only give access to sensitive data to authorized individuals who need it to do their jobs.
- Don't share sensitive information via email or other unsecured methods: Use secure file transfer methods when sharing sensitive data.
- Secure your devices: Ensure that your devices are password-protected and that you have security software installed.
- Report any suspicious activity: If you see something suspicious, report it immediately.
KEY FEATURES
Why you'll love our training
It’s time to embrace a new era of online training with a valued partner who will ensure seamless implementation, a truly enjoyable learning experience, and courses with continuous compliance you can trust.
Compliance expertise
Traliant's in-house legal expertise ensures training is accurate and kept up-to-date with any regulatory changes.
Accessible to users with disabilities
Traliant provides an inclusive experience for all users, including those with disabilities, by going beyond Section 508-C standards and offering WCAG 2.1/2.2 AA.
Story-based learning
Our story-based approach blends leading instructional design with Hollywood talent to produce engaging, interactive and nuanced training.
Course administration
Traliant makes it simple to roll out training to your workplace and provide technical support directly to your employees at no additional cost.
Course customizations
Tailor courses to include your logo, relevant policies, workplace images, and more. Traliant can even customize the course with scenarios that take place in your own workplace environment.
Translations
Training is available in English, Spanish and is supported in over 100 languages.
COMPLIANCE EXPERTISE
Your partner in training compliance

Uniquely qualified in-house compliance team
Our exceptional in-house Compliance Advisory Team is led by Michael Johnson, Chief Strategy Officer and former U.S. Department of Justice attorney who has provided training and guidance to organizations like the Equal Employment Opportunity Commission, Google, the United Nations, and the World Bank.

Keeping you compliant, effortlessly
Keeping up with the complex web of employment laws — especially if your workforce spans multiple states — can be tricky. That’s why we offer a streamlined training solution that ensures you stay compliant with federal, state, and local regulations, so you can focus on what matters most: your team.

Simplifying your policies and handbooks
Crafting an employee handbook that meets legal standards can be daunting. Let us ease the burden. We help you navigate regulatory changes to ensure your policies and handbooks not only comply with the law but also reflect industry best practices.
THE TRALIANT DIFFERENCE
Compliance you trust.
Training and solutions you love.

Legal expertise
Our in-house legal team is at the heart of our course development, writing content and ensuring compliance. As laws change, they provide real-time updates so you can trust your training is accurate and up to date.

Brilliant training
Each year we release brand-new, cinematic, Netflix-style courses with fresh stories, interactive scenarios, and industry-specific nuance. The result? A lasting impact on your culture and an experience employees will love.

Innovative solutions
With TikTok-style micro reels, advanced AI translations, phishing simulations, policy and handbook services, and analytics in one scalable platform, we make compliance simple and engaging now and into the future.

Valued partnership
Our main focus? It’s all about making your job easier. We do that with unmatched responsiveness and seamless deployment, dedicated to driving your success.




